Event POS Fraud Prevention: What Every Organizer Needs to Know

Key Takeaways
Event POS fraud prevention is no longer just a gate problem. The real risk runs through every payment terminal on your event footprint, and your payment architecture is the variable that determines how exposed you are.
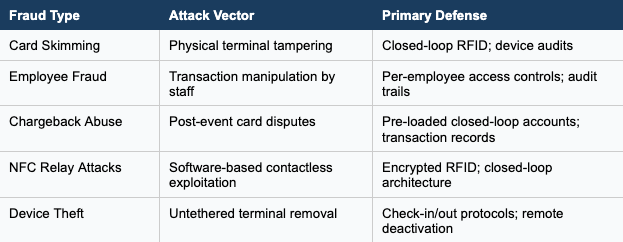
- POS fraud at events takes multiple forms: device tampering, employee theft, chargeback abuse, and NFC-based attacks targeting contactless terminals.
- RFID anti-fraud technology addresses the structural weaknesses of open payment systems by replacing static card data with encrypted, dynamic tokens that cannot be cloned or skimmed.
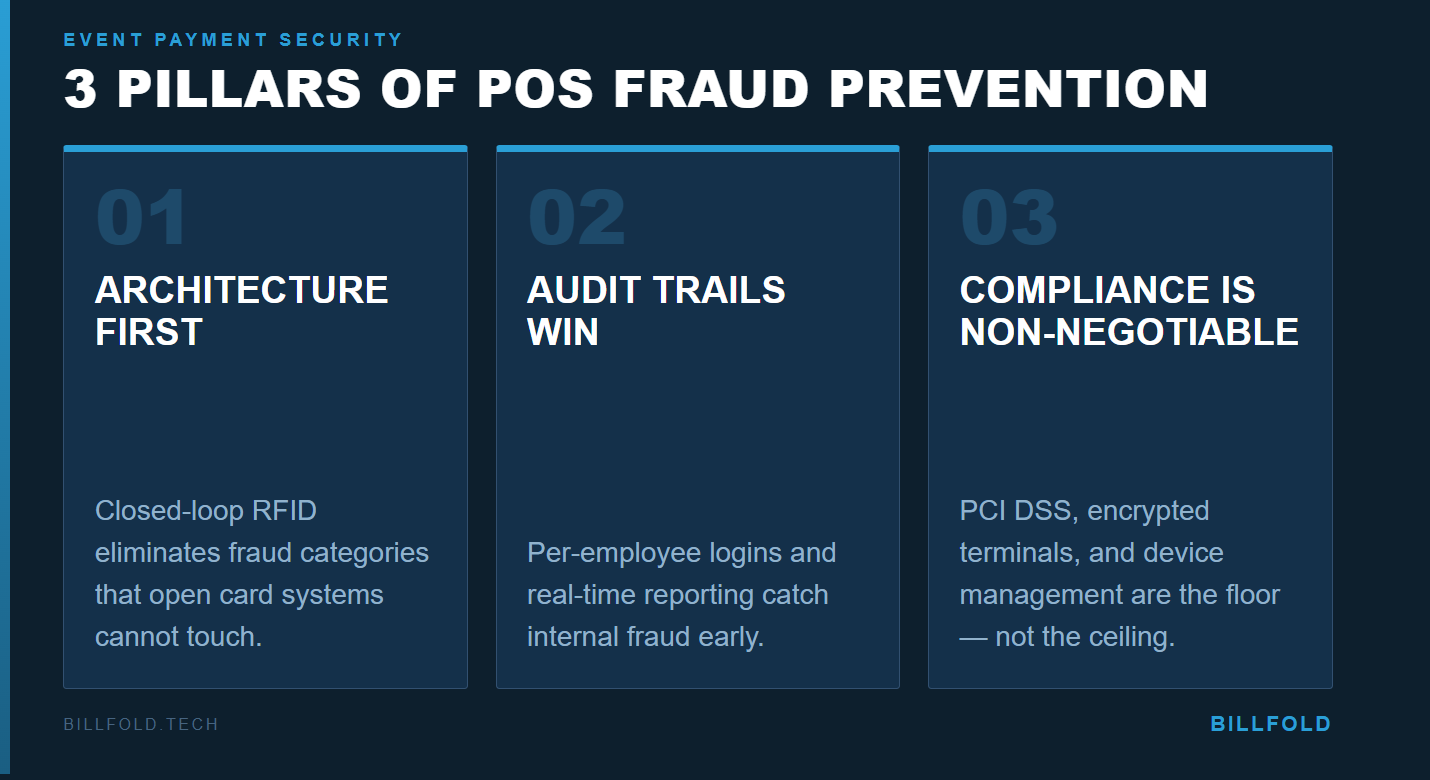
- PCI DSS compliance, staff training, real-time audit trails, and closed-loop cashless systems are the four pillars of serious POS system security at scale.
If your payment infrastructure was designed to process transactions rather than prevent fraud, you have a gap worth closing before your next event.
Most event organizers spend more time thinking about what happens at the gate than what happens at the bar. That is an expensive blind spot. While counterfeit tickets are a real concern, cashless fraud at the point of sale has become one of the most significant and least-discussed revenue threats in the live events space. Skimming techniques, employee-side manipulation, and NFC-targeted malware are creating vulnerabilities that low-cost card readers were not designed to handle. A January 2026 report from Infosecurity Magazine documented at least $355,000 in illegitimate transactions linked to a single compromised POS terminal vendor operating openly between late 2024 and mid-2025. That is one operator. The total exposure across high-volume festival and venue environments is far larger.
Event POS fraud prevention is a systems problem, not just a policy problem. The decisions you make when selecting and configuring your payment infrastructure determine how much surface area you give fraudsters. This guide breaks down the threat landscape, explains how modern payment architectures address each risk, and gives you a concrete checklist for hardening your setup.
What Is Event POS Fraud Prevention?
Event POS fraud prevention covers the technology, policy, and operational practice that protects payment terminals, transaction data, and revenue from fraudulent activity at festivals, venues, and live events. It addresses both external threats, like attackers targeting your payment hardware, and internal ones, like staff manipulation of transactions. Chargeback fraud is also in scope: an attendee disputes a legitimate purchase with their card issuer. Each attack vector requires a different mitigation strategy, which is why a single fix like switching to chip readers falls short in complex, multi-vendor environments.
Why Event Environments Create Unique POS Vulnerabilities
Events combine temporary staff, distributed vendor setups, and compressed operating windows. A vendor booth running hundreds of transactions per hour is not going to catch a skimming device mid-shift. A new hire bartender is not going to recognize a tampered terminal during rush. The distributed nature of event setups also multiplies physical touchpoints for tampering. Unlike a retail store with fixed checkout lanes, events run terminals across dozens of stations, each a potential compromise point, particularly when POS system security protocols are applied inconsistently across the event footprint.
What Are the Most Common POS Fraud Threats at Events?
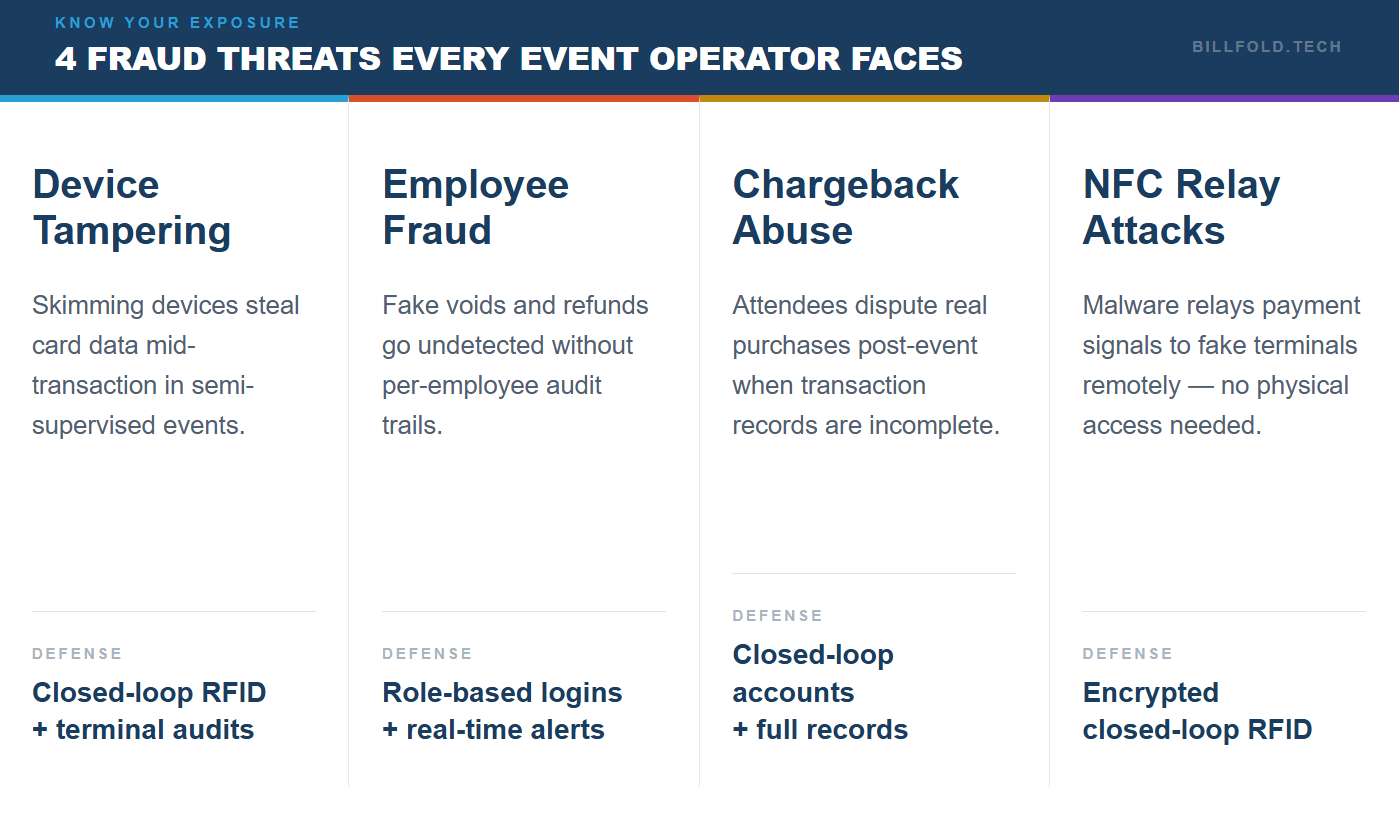
The threat landscape for event POS fraud is wider than most organizers realize. Here are the categories that matter most for festival and venue operators.
Device Tampering and Card Skimming
Skimming involves attaching an illicit device to a payment terminal to capture card data during a transaction. Security researchers have documented NFC relay malware targeting live POS terminals that can harvest card data for cloning or unauthorized transactions — with no physical contact required. In a crowded festival setting with semi-supervised vendor terminals, detection is difficult. Mobile POS devices create additional exposure: untethered handheld terminals can be pocketed and used fraudulently after the event. A device check-in and check-out protocol is a basic control that many events skip entirely.
Employee-Side Fraud
Internal fraud is a significant source of event payment losses and among the hardest to detect in real time. Common patterns include under-ringing transactions, voiding completed sales and retaining the payment, and processing fake refunds to a personal account. High staff turnover in event environments creates conditions where these behaviors go unnoticed for entire shifts. POS fraud research consistently identifies role-based access controls and per-employee credential logging as the primary structural defenses — without them, anomalous behavior is invisible until the post-event reconciliation, when the damage is already done. Digital audit trails are the fix: when every transaction, void, and refund is logged against a specific staff credential, anomalous patterns become visible in real time.
Chargeback Fraud and NFC Relay Attacks
Chargeback fraud occurs when an attendee disputes a legitimate transaction with their card issuer. Events are particularly vulnerable because transaction records are often incomplete and the response window does not align well with post-event administrative capacity. Closed-loop cashless systems reduce this exposure because attendees load funds onto an account rather than transacting card-to-terminal for each purchase.
NFC relay attacks represent a more technical threat. The Infosecurity Magazine investigation into Ghost Tap malware documented cases across multiple countries where criminals relayed NFC payment signals to physical terminals without the cardholder present. This cashless fraud vector requires no physical access to a terminal. Detections of tap-to-pay malware increased steadily from mid-2024 through late 2025. Event operators relying solely on NFC bank card acceptance inherit this risk, while closed-loop RFID systems insulate operators from it entirely.
How Does RFID Anti-Fraud Technology Change the Equation?
The architecture of your payment system determines your baseline fraud exposure. Open-loop systems, where attendees pay using their own bank cards at every transaction, inherit all the vulnerabilities of the broader card payment ecosystem. Closed-loop RFID systems, where attendees pre-load funds onto a wristband or account that only works within your event environment, structurally reduce that surface area. RFID anti-fraud is a property of the architecture, not a feature you bolt on afterward.
Encryption, Tokenization, and Wristband Controls
RFID payment systems communicate using encrypted, dynamic tokens rather than static card numbers. Each transaction generates a unique cryptographic exchange between chip and reader. Even if a signal were intercepted, the data would be meaningless without the decryption key. Tokenization ensures the actual account value is never exposed at the point of transaction. At the wristband level, each device carries a unique identifier tied to a specific attendee profile. If a wristband is lost or stolen, it can be deactivated instantly and funds transferred to a replacement. These wristband security controls also let organizers set spending limits and maintain a real-time ledger per attendee. RFID chip cloning requires equipment whose cost far exceeds the value of a typical event payment account.
What Does POS System Security Look Like in Practice?
Technology sets the ceiling on your fraud protection. Operations determine how close you get to it. Even sophisticated hardware will not protect you if terminals are left unattended, credentials are shared, or reconciliation happens days after the event.
PCI DSS, Staff Controls, and Real-Time Reporting
PCI DSS (Payment Card Industry Data Security Standard) sets minimum requirements for how businesses handle cardholder data. For event operators, this means certified terminals, encrypted data in transit and at rest, and controlled, logged access to payment systems. Encryption and compliance standards are a first line of defense across any multi-vendor event footprint. Non-compliance can result in fines and loss of card processing capabilities.
Temporary staff are the highest-risk access point in event payment operations. Per-employee login credentials and role-based permissions that restrict what each role can do are the structural fix. Mobile POS devices should be logged in and out by shift with a designated responsible party. Any unaccounted device should be treated as a security incident until resolved.
Real-time transaction monitoring is one of the most underused security tools at events. Modern venue POS platforms surface anomalies as they occur: unusual void rates, refund patterns outside expected norms, or transaction volumes inconsistent with a vendor's location. Waiting until post-event reconciliation means the loss has already happened.

6 Steps to Strengthen Event POS Fraud Prevention
These steps apply regardless of event size or how mature your current payment setup is.
- Audit terminals before every event. Physically inspect each POS device for tampering or unfamiliar hardware. Train staff to flag anything that does not match the standard setup.
- Move to per-employee access controls. Shared credentials make internal fraud impossible to attribute. Role-based logins create accountability and make transaction anomalies actionable.
- Set up real-time transaction monitoring. Establish thresholds for void rates, refund volumes, and transaction velocity per terminal. Any station outside normal parameters should trigger a same-shift review.
- Evaluate closed-loop RFID for your architecture. For high-volume events, the structural fraud reduction of a closed-loop RFID system eliminates entire risk categories that open card-based systems cannot address.
- Lock down device management. Log every mobile terminal in and out by shift. Treat any unaccounted device as a security incident until resolved.
- Confirm PCI DSS compliance before opening day. Verify every terminal in your footprint is certified, data transmission is encrypted, and your payment vendor holds current compliance certifications.
How Do Cashless Payment Architectures Compare on Fraud Risk?
Your payment architecture is the highest-leverage security decision you can make. Here is how common event setups compare across key fraud risk dimensions.
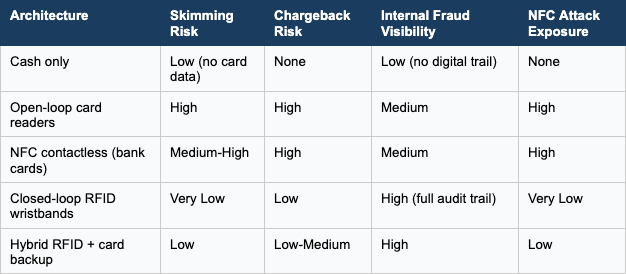
No architecture eliminates all fraud risk. Cash has no digital footprint but creates its own theft and reconciliation problems. Open-loop card systems are convenient but inherit the full consumer card threat landscape. Closed-loop RFID sits in the most defensible position across the risk categories that matter most, particularly at scale.
FAQ
What is the biggest fraud risk at festival and venue POS systems?
The most common threats are card skimming, employee-side transaction manipulation, and chargeback abuse after the event. NFC-based relay attacks represent a growing category, particularly as the toolkits for this type of cashless fraud have become more accessible to bad actors.
Does switching to cashless payments prevent fraud at events?
Cashless systems reduce several fraud vectors significantly, including cash theft, employee skimming, and chargeback exposure. Open-loop systems that accept standard bank cards still inherit NFC and card-skimming risks. Closed-loop RFID systems offer meaningfully stronger protection because the architecture removes the most common attack surfaces rather than adding defenses on top of them.
What is PCI DSS and does it apply to event operators?
PCI DSS (Payment Card Industry Data Security Standard) applies to any business processing, storing, or transmitting cardholder data. If your event accepts credit or debit cards at any point, these requirements apply: certified terminals, encrypted data, and controlled access to payment systems. Non-compliance can result in fines and loss of card processing capabilities.
Can RFID wristbands be hacked or cloned?
Modern event-grade RFID chips use encrypted communication protocols that make intercepted data unusable without the correct decryption keys. Cloning requires specialized equipment whose cost significantly exceeds the value of typical event payment accounts. Lost or stolen wristbands can be deactivated instantly, with funds transferred to a replacement.
How do I catch employee fraud at a large event?
Per-employee login credentials, role-based access controls, and real-time monitoring of void and refund rates by terminal and operator are the most effective tools. Any pattern outside expected norms should trigger an in-event review. Post-event reconciliation comparing sales records against inventory and net revenue will surface most anomalies that were not caught in real time.
The Organizer Who Gets This Right Keeps More Revenue
Event POS fraud prevention does not get enough attention because the losses are often invisible. There is no single moment of failure. There are dozens of small exposures across a large operating window that add up to a real drag on revenue and a genuine risk to attendee trust. The events that handle this well are not doing anything exotic. They are choosing payment architectures that reduce structural exposure, running the operational controls that catch anomalies early, and treating security as a first-order decision rather than an afterthought.
Billfold is built for exactly this environment: high-volume, multi-vendor events where payment security and operational speed need to coexist. With closed-loop RFID payment technology, real-time reporting, per-operator access controls, and end-to-end encryption, Billfold gives event operators the infrastructure to run a genuinely secure payment environment without slowing down the experience. If you are ready to close the gaps in your current setup, reach out to the Billfold team to learn how.

